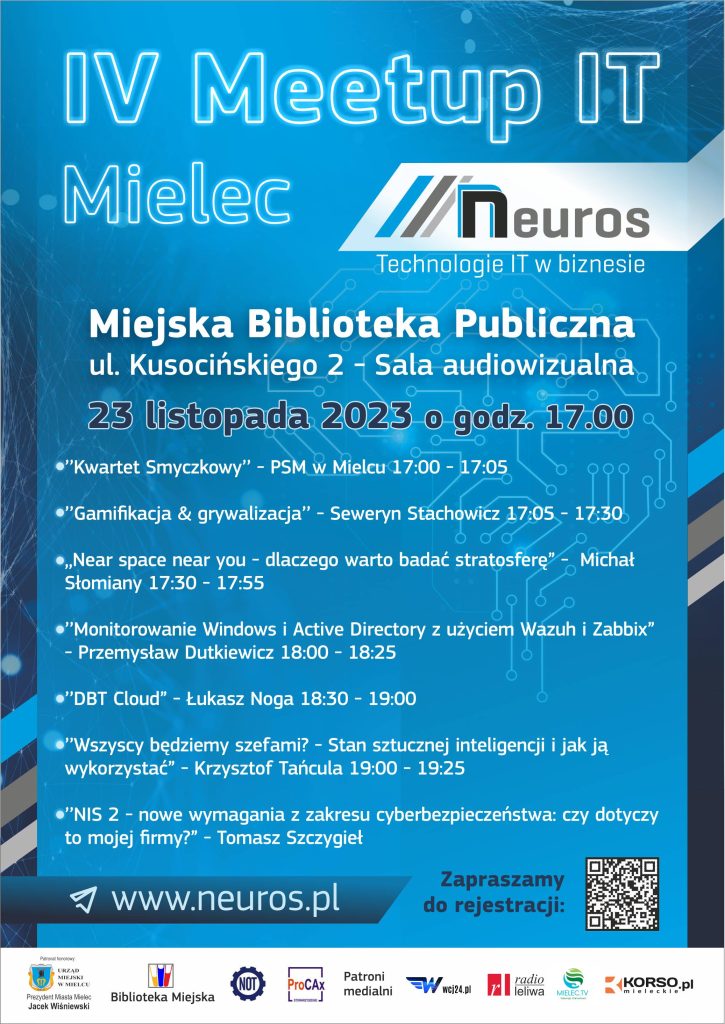
IV Meetup IT Mielec
In 2006, the first “UN IGF Summit” was held in Athens.
This time, for the first time in Poland, the UN Digital Summit.
People from all over the world who are interested in the proper development of IT technology.


The promotion of security in the reality that surrounds us is a topic that should always receive attention.
The growing amount of data already referred to as the “data deluge” will increase, having data means being able to analyse it.


Network security – phishing – Sylwia


Data and its value – Seweryn
We conducted a lecture about security for business in Mielec Read More »
Carpathian Startup Fest 2021 (first carpathian festival for start-ups)
The festival shows that creating reality is done by all of us.




We participated in Podkarpackie Carpathian Startup Fest 2021 Read More »
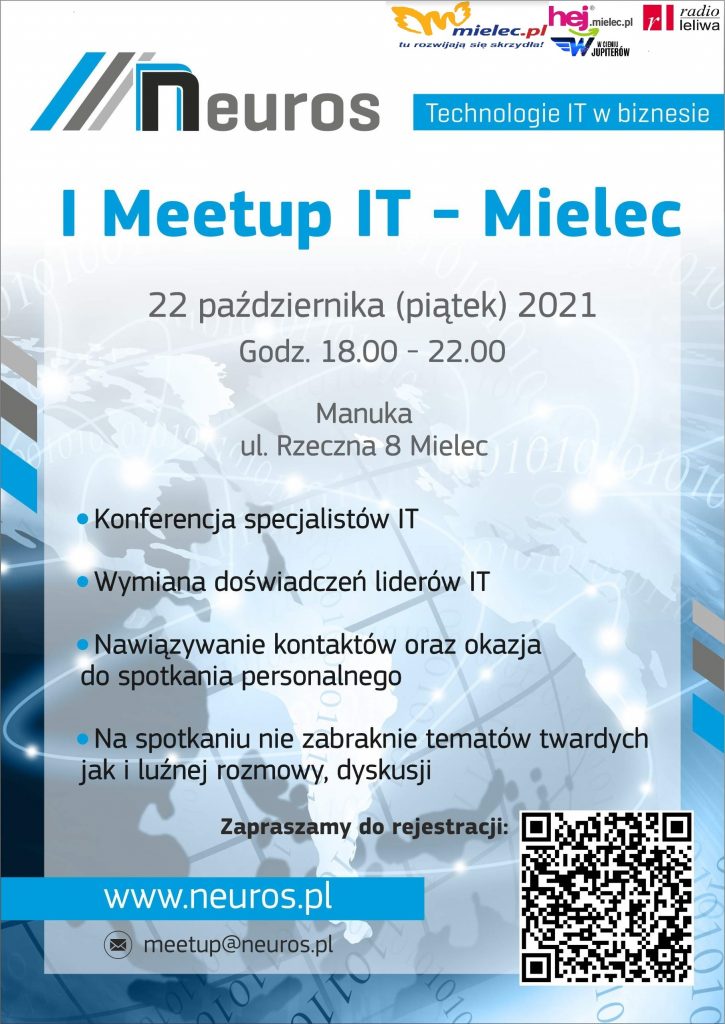
We would like to thank all the speakers and all those present.
We invite you to the next meetings.








Link to agenda (registration form):
https://www.meetup.com/Meetup-Mielec-IT/events/280987596/
Abbreviated agenda:
(18:00) Welcoming the assembled guests Joanna Stachowicz
(18:05) Short concert performed by a string quartet from the State Music School in Mielec – Ryszard Kusek Ph.
(18:20) Lecture – “Information Technology in the Polish industry – development and current European Funds FENG 2021-2027” – Wlodzimierz Adamski Ph.
(18:35) Lecture and discussion – “Empathy in IT” – Seweryn Stachowicz
(19:30) Lecture and discussion – “Data Lakes” – Łukasz Noga
(20:00) Lecture and online panel – “10 years of living with the cloud – what have we learned from cloud deployments in Europe and the World!” – Michał Furmankiewicz
The event was held under the Honorary Patronage of the Mayor of Mielec – Jacek Wiśniewski.